Pharming: another reason to think before you click


Cybercriminals take advantage of people’s carelessness to obtain passwords, ID numbers, home addresses, bank accounts and other personal information. Straying onto a fake website is one way they do it. This article explains what “pharming” is and how to spot and prevent it.
Imagine you’re in your car on your way to a house in the country to spend a few days on holiday. You follow all the directions for getting there, including a right turn that, without realizing, steers you away from your destination. You end up somewhere and don’t know why nor how you did. That’s how “pharming” works online. It’s a trick in which legitimate websites or servers are tampered with to redirect users to fake websites that capture their personal info or even their money.
“Pharming” is the portmanteau of “phishing” (i.e. impersonation on email or text messages) and server “farms” that redirect users to fraudulent websites.
Whether you're an Internet amateur or expert, the key to understanding this scam lies in how you browse online. To visit a website, you normally write its address in the browser or click on a direct link. The browser turns the information into a numerical Internet Protocol (or “IP”) address for a specific server to show the website's content. Internet browsing works this way because a name is much easier to remember than a set of numbers.
Cybercriminals are on the lookout to make sure you don’t open the website you want and take you to another they've created to scam you. Knowing how they do it is the first step in avoiding their ploy. So let’s take a look at two ways they engage in “pharming”.
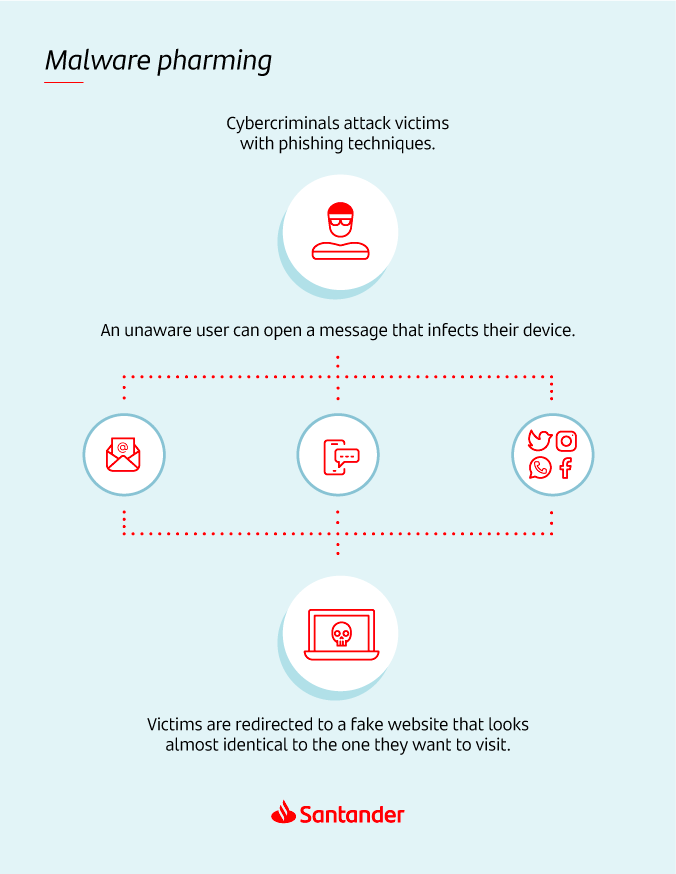
Malware pharming
Malware pharming involves an email, social network, SMS and other methods with a link or file that infects your device with malware (a harmful code) that contains false information and redirects you to a fraudulent website designed to look real and trick you into browsing it and providing your name, email password, bank credentials and other information.
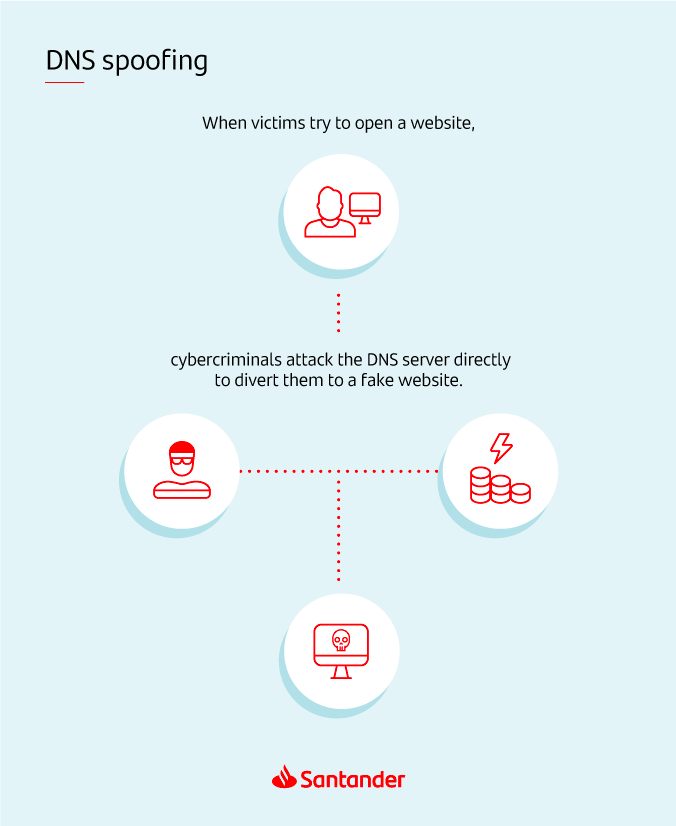
DNS spoofing
DNS spoofing is a cyberattack that targets Domain Name System (DNS) servers and not a user’s browser. The DNS receives and processes commands sent from devices connected to the same network. Therefore, DNS spoofing redirects users of a server infected with malware to fake websites controlled by cybercriminals.

How to spot pharming
In general, the best way to stay safe from such Internet scams is to be cautious with the information you receive or share via email or social media. Don’t forget: Santander will never send you emails or messages on social media asking you to share personal info or open a link. Therefore, think before you click or reply.
Also, you can follow these three easy but effective steps to make sure you’re browsing a website run by your bank:

Check the web address
A fake website’s address is usually very similar to the real website, save for a subtle difference that can be hard to notice at first, such as a dash between words or special characters instead of letters (like using “rn” to look like an “m”). At first glance, it might seem easy to notice; but when you open a fake website with the same display and colours as the original, you’re more likely to miss it.

Make sure the connection is secure
If the web address starts with “https”, it means the connection is secure (the “s” means “secure”) and your personal data being processed is protected. Otherwise, if the website only starts with “http”, it means the connection is unsecured and the website might not be legitimate.

Pay attention to the details
Because you visit your bank’s website often to make transactions, you should stop and follow the two recommendations above to make sure you’re not on a fake website if its display appears strange or unfamiliar (odd colours, misplaced buttons, strange font and other things).
You can also use a security or antivirus program to protect your device from malware. Plus, you should update the operating system on your computer or mobile phone to correct the security errors or weaknesses of older versions.







