Identity theft: how to detect and combat it


20/02/2023
A common practice among cybercriminals is the impersonation of well-known companies and people. They obtain your personal information to use it illegally and to commit fraud. They can also steal information from big or small companies to impersonate them and try to deceive you. Learn how to spot some of the most common ways identity can be stolen.
Identity theft as a crime isn't anything new, but as social media, e-commerce, dating apps and the entire digital universe grows, the risk of a third party impersonation of your persona online only increases. Put simply, identity theft is the unauthorised and ill-intentioned use of your personal data by someone in order to act under your name.
You might think that public figures like artists, politicians or athletes, are the only ones exposed to this type of crime. Nevertheless, cybercriminals will try to impersonate any identity that allows them to commit digital fraud, such as payments and online shopping, or even try to access information that helps them run scams.
How can you identify identity theft?
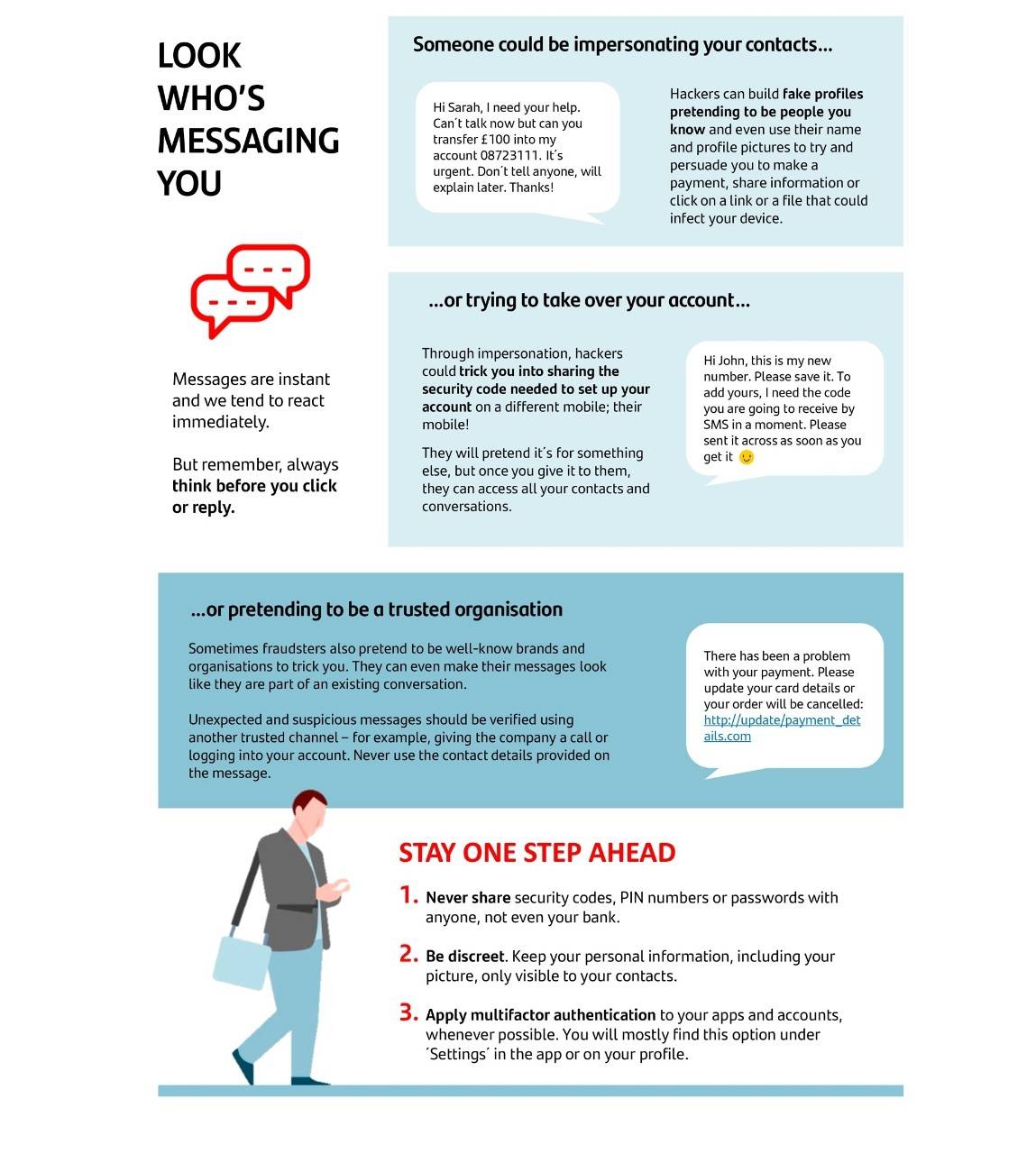
Imagine that, one day, you receive an email in your inbox, a text message on your mobile phone or a call from someone who claims to be a (generally well-known) company, such as your electricity company, or even your bank. There's always the risk that a scammer could impersonate a company, or third party, to gain access to your personal information. Before clicking on the link, answering any questions or providing your personal data, we recommend that you follow the recommendations below.
When you receive a communication of this nature, the first thing you need to do is to be prepared and question whether you have hired any services or bought any products from this supposed company. Other things to consider is if whether this is how the given company usually communicates with you, whether you have shared your contact details or whether there are any inconsistencies that look suspicious.
Make sure that the email address or social media account you are being contacted by are official channels of communication and clearly identified. If you're on the phone, remember to check any and all information you think is necessary to confirm that the other person is who they say they are.
Are they asking for your data over the phone? Should you click on an unknown link? Companies you have hired services or bought products from will not ask you for personal information, as they already have it.
If you make it this far, but you're not sure whether it's genuine, it's best to end the call or ignore the message. You can contact the company directly to check whether the communication did in fact come from them. m. Make sure to always use trusted contact details and never those that have been given to you or are included in a suspicious communication.
Tips on how to prevent identity theft
So far, we've discussed when companies or a third party have their identity stolen to lure you into a trap. However, cybercriminals could try other ways to deceive you or even steal your own identity.
Generally speaking, the main recommendation is to always remain cautious — the less information you share, the more difficult it will be for criminals to impersonate you. You can also take additional measures to enhance your cybersecurity when you are online, use electronic devices or pay using your bank card in the supermarket, among other everyday activities. Before you dive straight in, below is a list of some of the most common means of identity theft and what you can do to prevent falling victim to this type of fraud.

Criminals want to steal your card details to withdraw cash or charge purchases to your account. One such method is cloning the card itself when the victim uses it in a fraudulent device that stores the information, also known as skimming. Fraud can also be committed online through links or malware that steal your personal and financial information.
In both cases, the main course of action you can take it to always buy from trusted retailers (both online and physical), never tell anyone your card's security code or leave it out in plain sight, always carry your card on you or turn on notifications on your mobile phone so you're kept up to date on all banking transactions.
This method, known as 'swapping', is when the criminal, after obtaining some of your data, such as your name, personal identity number or telephone number, asks for a duplicate of your SIM card to gain access to the information on your device — this includes any messages you receive containing verification codes and passwords for your apps (e.g., banking).
If you notice that your calls cut out, your internet is down or your SIM card has been disabled, ask your phone provider for information to find out whether someone has asked for a duplicate card. To prevent this type of fraud, never share your phone number publicly on social media or online forms, for example.
Evidently, scammers use a whole host of methods to get hold of your data and access your email, social media accounts, banking apps, etc., and act under your name. Criminals could also use any of your data (name, telephone number, alias, photographs, user account, etc.) to create fake profiles or could hack your genuine profiles through techniques known as phishing.
Configuring security and privacy preferences on your apps and devices, staying alert regarding information that is public, never sharing your login details with anyone, activating two-factor authentication whenever possible, never sharing data with websites that do not start with 'https' or that do not have a padlock in your browser's address bar, are just a few measures you can take to safeguard your online identity from cybercriminals.
Identity theft can be a minor inconvenience or cause major disruptions. As such, the first step in to detect and combat this type of crime is to acknowledge that it exists and adopt the relevant security measures. Every step counts towards protecting yourself from online identity theft by cybercriminals.







